Email Protection
%2520(1).avif)
%2520(1).avif)
Picture this for a moment. Your finance manager is in a meeting. A message lands in their inbox. It looks like it came from you. The tone is right. The timing makes sense. It asks for an urgent payment.
Within minutes, £7,000 is gone. Then another. And another. By the time anyone questions it, the damage is done. I have sat across the table from directors in the North West as they relived that moment. The loss is never just money. It is confidence. It is trust in systems that were meant to protect them.
Email Protection is about putting calm, intelligent controls around the busiest doorway in your business. We start with a careful discovery phase. We map your network, review access rights, and run credentialed scans using Kaseya 365 and Connect Secure. Not to tick boxes, but to uncover real exposure.
Then we prioritise what matters. Misconfigurations, insecure protocols, outdated firmware, weak policies. You receive clear, presentation-ready reports that make sense to both your technical team and your board. If something critical is missed and found within 30 days, we return and audit again at no cost. You deserve thoroughness, not guesswork.

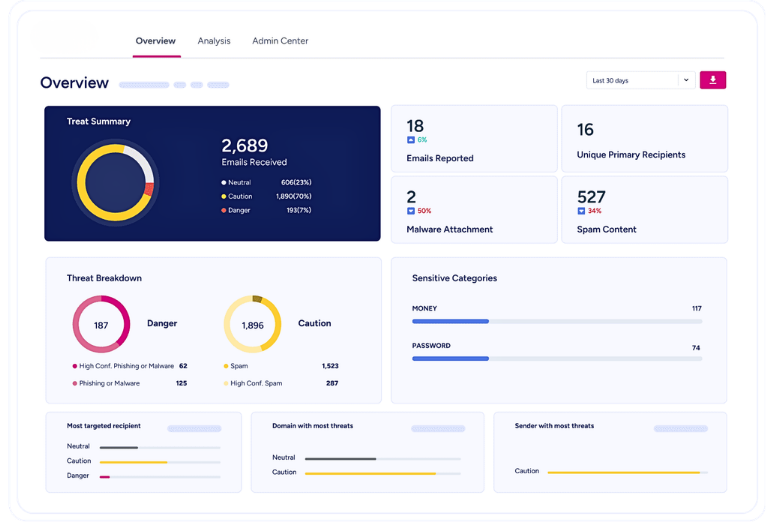
At its heart, Email Protection examines every message before your team ever sees it. It checks who truly sent it. It inspects links and attachments. It watches for patterns that suggest impersonation or account compromise. Suspicious emails are quarantined. High-risk actions are flagged.
But strong protection goes deeper. We review firewalls, servers, routers, switches, and endpoint devices. We assess encryption standards, VPN settings, and access controls. We align your setup with recognised frameworks such as ISO 27001, NIST, and Cyber Essentials. The outcome is simple and powerful: fewer successful attacks, clearer accountability, and a workforce that can act with confidence instead of caution.
AdaptiveComms was built in Southport with a clear belief. Technology should be understood. Risks should be explained plainly. Decisions should be based on evidence. Demystifying tech is not a slogan for us. It is a responsibility.
A media company in Manchester lost £21,000 to a spoofed email, the real blow was reputational. Staff numbers fell. Clients walked away. When they came to us, we identified the gaps quickly: no spoof protection, no managed detection and response, no structured cyber training. We put those layers in place. With the right controls, that fraudulent email would never have reached their inbox. Today, they operate with resilience and oversight, not fear.
If you lead a business with 40, 80, or 150 users, you carry enough weight already. Email Protection should remove burdens, not add to them. If you would like a clear view of your current exposure, let’s have a straightforward conversation. I will tell you what I see, and what I would do if it were my own business.

Ready to shed the weight of tech worries? Click here to start a conversation with an AdaptiveComms expert today. We’re not just offering a service; we’re extending a partnership for seamless operations. Don't let tech troubles dim your sparkle. Let’s join hands and turn those tech challenges into triumphs.
Choosing the right partner for Email Protection is a trust decision. AdaptiveComms brings structured audits, rapid response times, and clear accountability to businesses across the UK. We focus on measurable risk reduction, compliance alignment, and protection that stands up under pressure.
If you suspect gaps in your Email Protection, you are probably right. Let us review your environment properly. We will assess configurations, access controls, spoof protection, and monitoring. Then we will show you, in plain language, where you stand and what to fix.
Click the button. Book the conversation. Get answers grounded in evidence, not assumptions.